Securing a web application is not a one off job which needs to be undertaken while developing the web application, but also something that needs ongoing efforts. This is because we are dealing with a dynamic environment or an ever evolving landscape of technologies. As these technologies are adopted by web developers it allows attackers to find new vulnerabilities within web applications and use them to their advantage.
Foundations of Security
•Authentication- Authentication deals with who the user of the web application is?
•Authorisation- Authorisation deals with the level of access that a particular user has to a web application. E.g. files, tables, databases etc.
•Auditing- Auditing deals with creating systems within web applications that can track events. Effective auditing and logging is the key to non-repudiation.
•Confidentiality- Confidentiality deals with protecting information on the system. The aim is to keep the data private and confidential and as such secure from unauthorised users. Encryption and Access Control Lists are commonly used techniques for maintaining confidentiality in web applications.
•Integrity- Integrity involves ensuring that the data shared across a network is consistent, accurate and trustworthy. Some data might include checksums, even cryptographic checksums, for verification of integrity.
•Availability– Availability deals with the regular maintenance of the system hardware and related software with the aim of keeping the system up and running at all times. This also involves preparing a fast and efficient plan for disaster recovery if the need be.
Some of the most common web application attacks include;
DDoS Attack– An orchestrated attack in which a number of compromised machines (computers) are used to bring down a single target, a website, a web application or a server by overwhelming its network with traffic. Servers are usually built to handle a particular amount of traffic and if this line is crossed then it may cause a system to slow down or even break. This affects the capability of genuine users over the network to access the web service.
Brute Force Attack- A trial an error method whereby an attacker tries different combinations of usernames and passwords with the aim of gaining access to the website or web applications administrator panel. Due to the nature of these attacks the memory of the server where a web application goes through the roof and this might cause a disruption in service.
SQL Injection Attack- A form of attack whereby the attacker tries to get access to the database (SQL) of a website or a web application by injecting malicious code or SQL statements into an input field.
Cross Scripting Attack (XSS)- A form of attack that is aimed at attacking users visiting a website. This is a browser side attack and is executed by sending out a malicious code to a website or a web application. XSS attacks occur when a website or web application that accepts user inputs and does not encode or validate the output it generates.
Inclusion Vulnerabilities- In this form of an attack, hackers try to attack a website or a web application by finding insecurities in its source code. They can either execute a code that is part of the web application or execute a code located at a remote location.
There are two types of Inclusion Vulnerabilities-
- Remote File Inclusion (RFI) – This type of intrusion is executed using the ‘dynamic file include’ mechanism of a web application. The vulnerability allows attackers to trick the system or web application into running a malicious code located on remote files.
- Local File Inclusion (LFI) – Similar to a RFI attack with the only difference being that the malicious code that needs to be executed has to be present on the local server.
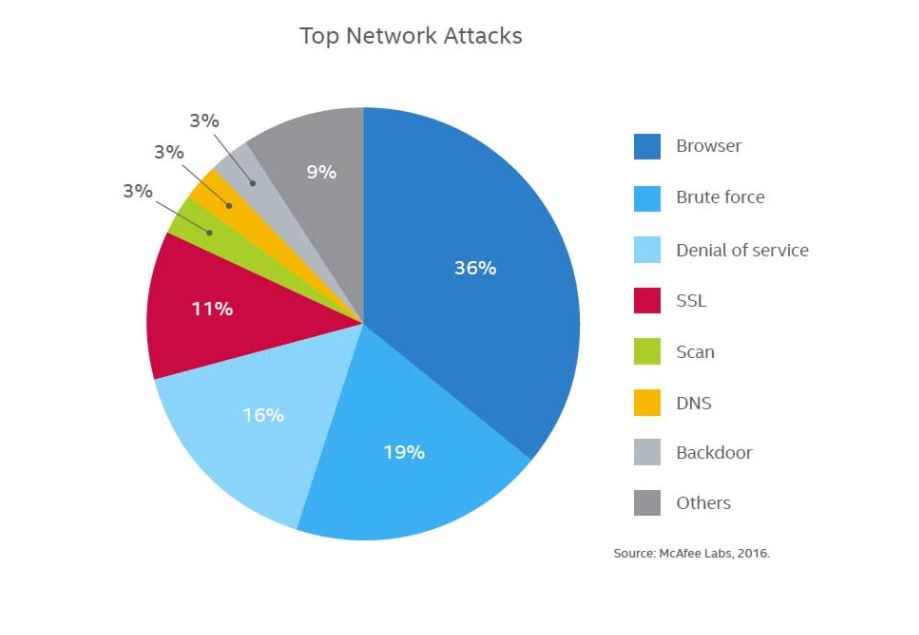
Data on Web Attacks For Quarter 4, 2015
The following types of attacks were reported by McAfee Labs Threat Report in 2016;
Browser Attacks 36%
Brute force attacks – 19%
Denial of service attacks – 16%
SSL attacks – 11%
Port Scans – 3%
DNS attacks – 3%
Backdoor attacks – 3%
Building a Secure Web Application
As pointed out by Microsoft in one of its articles, In order to secure a web application, web developers need to take an overall view of the infrastructure that is responsible for running the web application. This includes;
1- The Network
2- The Host or Server
3- The Web Application
1- Securing the Network- The network infrastructure plays a critical role in securing the web application. The network infrastructure consists of routers, firewalls and switches. A secure network is responsible for ensuring the integrity of the traffic that it is forwarding and since this is the outer most layer in the overall infrastructure, it is important that security threats (ports, protocols or harmful communication) that are known are dealt with at this layer.
2- Securing the Host/Server- The best approach to securing a server is to breakdown the various components/settings and use a systematic approach to mitigate risk for each of the components. This includes,
• Updating the OS version and applying security patches as and when they are released.
• Using log monitoring to determine any unusual activities.
• Taking timely backups of the files and the database on the server.
• Disabling unused services on the server.
• Limit access to files to the bare minimum.
• Setting up a Intrusion Detection System (IDS), this will provide alerts if any of the files on the server are changed.
• Monitor system performance and keep a close eye on bandwidth. If a system does become compromised you will notice an unusual spike in the bandwidth usage.
3- Securing the Web Application- In order to secure a web application it is best we identify and categorise the risks that web applications are commonly subjected to and work towards developing web applications using proven methodologies that mitigate such risks.
• Input Validation
• Authentication
• Authorisation
• Session Management
• Parameter Manipulation
• Exception Management
• Auditing & Logging
• Configuration Management
The truth is businesses do understand the risks of having a presence in the virtual world but they fail to address these risks and this is partly because of the fact that they find it difficult to quantify the direct benefits of doing so. A lot of times business take a more pro-active approach to security once they have had a website or an web application compromised. Hopefully you found this information useful!
About Us
Websites ‘N’ More is a web development company based out of Sydney, Australia. We have extensive experience developing PHP based websites and applications.